Enhanced System Security

Enhanced System Security helps to prevent any issues before they occur, OPS-COM has standard security features for risk management, as well as offers additional access to enhanced security options and training to implement best practices for parking and security departments.
OPS-COM was designed with security in mind. Dealing with credit card and personal details were always topping the priority list in the evolution of the OperationsCommander parking and security platform software.
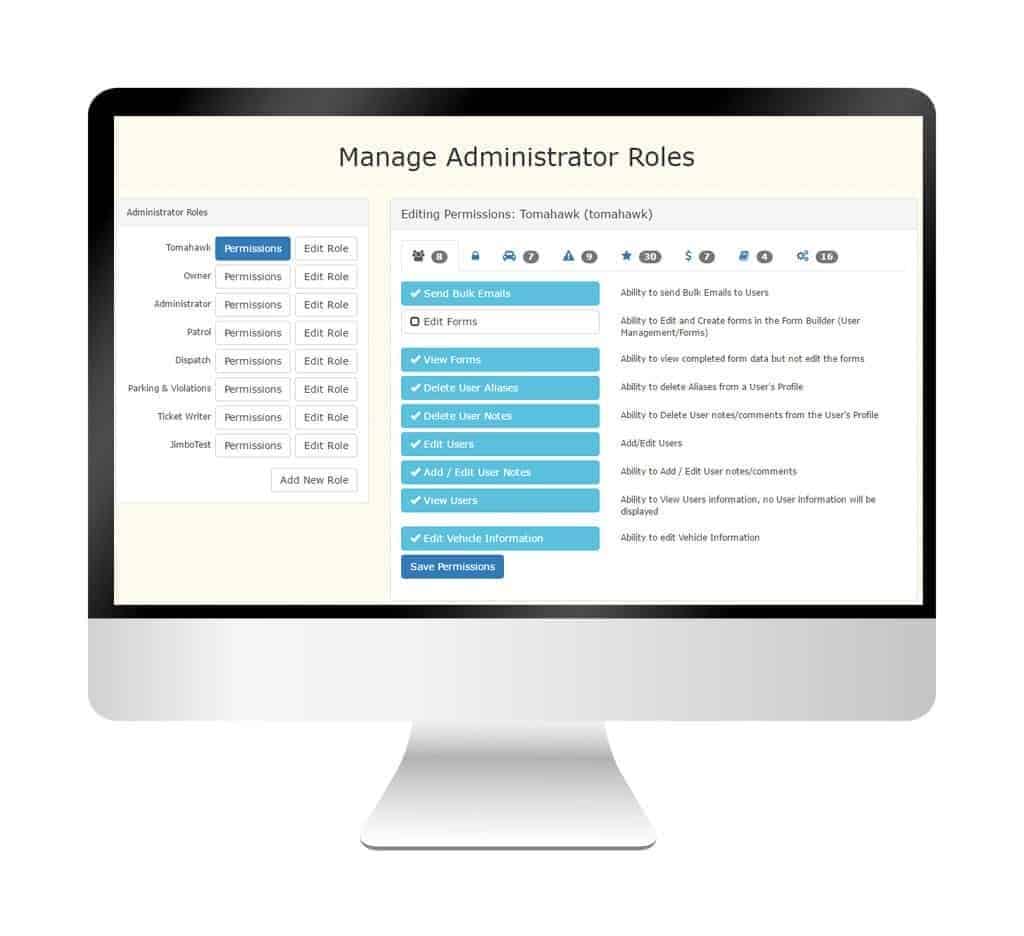
Security was not only developed to keep clients safe but to also keep staff safe as well. Many features within the system help to ensure that staff does not accidentally overstep their bounds, or in the case of sharing a password that it is not exposed to other staff members.
With full audit trails as part of the system, reports can be generated to review how clients transitioned through the system. From a corporate point of view, this helps to remove liability as everything is stamped with a date/time and also the person performing the action. In some cases, comments are required elements when the system determines that it is necessary.
Enhanced System Security
OperationsCommander offers a complete turnkey approach to system and client security. We offer out-of-the-box security and also offer heightened security with many options to fine-tune and configure your system to match your business rules. System administration and related security is a primary focus to ensure stability and security for your users.
With any standard OPS-COM install your data is protected and secured with these features:
Secure SSL Encryption
We use an SSL protocol to deliver a secure link between your OPS-COM system, your clients, and our servers. All data is encrypted and protected. We are PCI compliant and maintain this status through third-party scans and self-assessments.
Secure SSL is the same technology that is used by financial institutions and most systems that deal with personal information. Over the coming years, SSL will become a widespread requirement for site interaction. SSL ensures that the content producer is the expected entity and wraps a layer of security around communication between the end user and the server.
Hosted Payment Delivery
OPS-COM utilizes hosted payments which alleviate strict PCI compliance guidelines for organizations and reduces the risk of financial information falling into the wrong hands. Hosted payments also add the additional option of debit payment for one of your payment options. In all cases, OPS-COM is compatible with most payment providers including: TouchNet, CHASE PaymenTech, Moneris, PayPal and Authorize.net
OPS-COM does also support payment gateway implementations. Such support is required for subscriber-based payment systems. As an example our Text2ParkMe solution allows users to pay for parking using standard text messaging. Payment details are stored on the server and used during the final processing of payment. This ensures that no credit card details need to be supplied during the transaction process.
Password Encryption
Hashed and salted encryption methods prevent passwords from being read, copied, or reverse-engineered. Often users re-use passwords across many devices and platforms, by hashing or encrypting passwords we ensure that passwords are not accessible.
Even the most secure password isn’t all that secure if it is used in more than one place. With OPS-COM the plain text version of a password is not stored, and when a new password is supplied the value is hashed and the result is compared against the stored value. This prevents administrators from having view access to user passwords that could have been re-used on other systems.
It is a big inconvenience to have to completely reset a password when an old password is forgotten, but security is simply necessary in our connected world.
Secure Password Delivery
Password resets are completed via a secure link and never emailed. Users control the password reset process and the process never involves the transmission of a user password with plain text.
Password resets must be completed through system automation. This removes any chance that staff may see or copy passwords from the system. Even a user that re-uses a password on many different systems is secure knowing that the administrators on OPS-COM do not have access to the password. Organization managers are happy to know that their liability is reduced in this area.

Available Security Options and Training
Companies looking to bring added security to their system to support strong risk management to limit liability. These security enhancements reduce the potential impact of a security breach that gives organizations peace of mind. These enhanced security protection and training options include:
Account Audit
Regular account audits help you understand the accounts you have set up in your system, what information they have access to, and how they are used. These audits show you where people might have access to information they shouldn’t, users who have an irregular log in or use patterns, and IP trends that might be a signal of potential threats.
Password Strength Requirements
Configure your password requirements so users must create strong, less vulnerable passwords. Set a minimum number of characters, and requirements for letters and symbols, and prevent the username and password from being the same.
Password Expiry
Set your limit for how long a user can keep a password. We’ll provide advice and guidance on how to configure this specifically for your organization.
Lockout Protocol
Create your limits for the number of attempts at logging in before a user is locked out. You can also create lockout protocols for specific IP locations or account criteria.
1-Hour Employee Security Training
So you don’t have to develop your own training, we’ll deliver a session on the importance of the new security features and why a password policy is critical, how roles will affect permissions especially as they relate to their responsibilities. Plus, we’ll provide webinar access to future training for staff.
Get a Copy of Our Parking and Security Brief
[wpforms id=”866″ title=”false” description=”false”]
